DocsEdge Stack
1.14
Consul integration
Consul integration
Contents
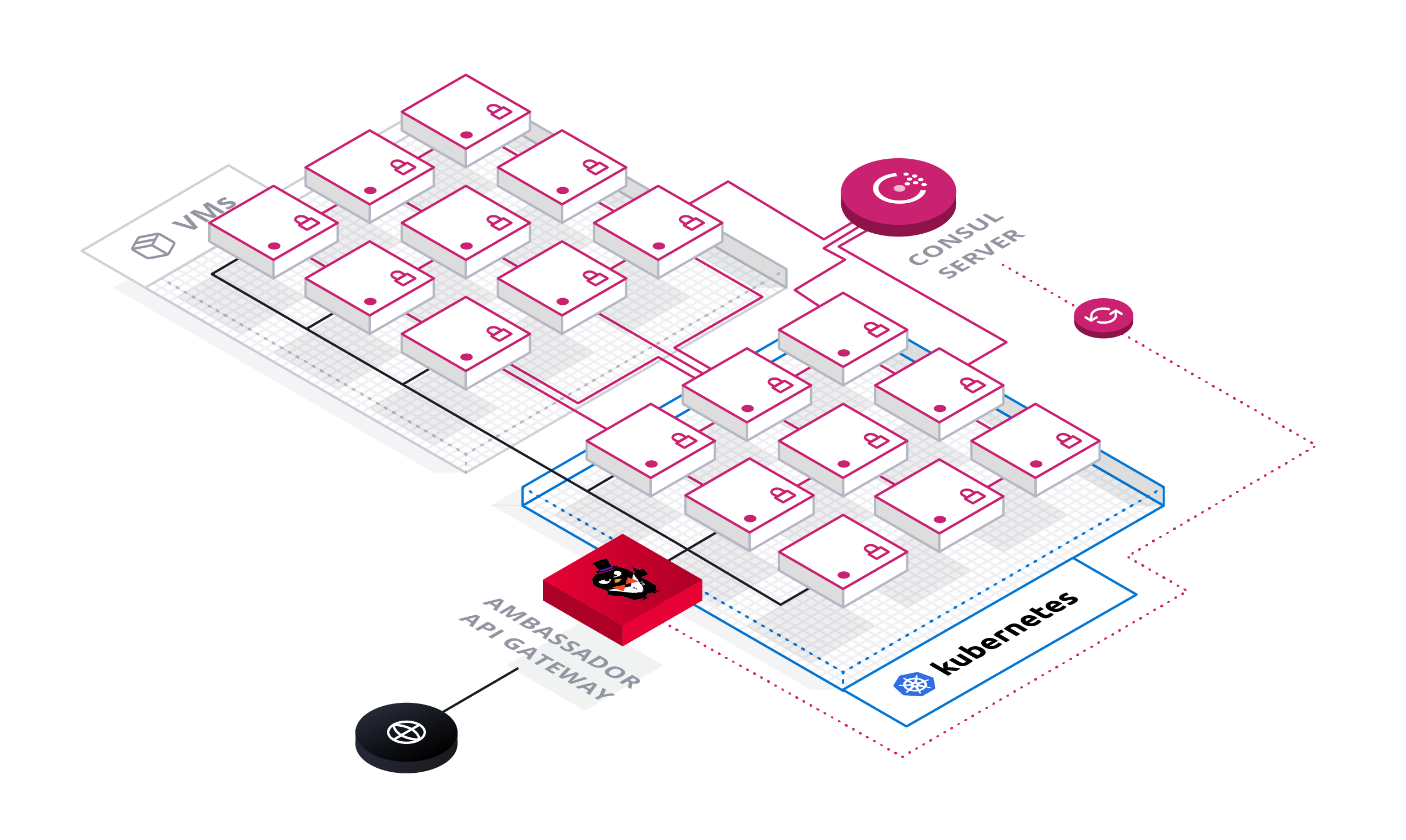
Consul is a widely used service mesh. You can use Consul with Ambassador Edge Stack, as it natively supports Consul for service discovery and end-to-end TLS (including mTLS between services). This capability is particularly useful when deploying Ambassador Edge Stack in so-called hybrid clouds, where applications are deployed on VMs and Kubernetes. In this environment, Ambassador Edge Stack can securely route over TLS to any application regardless of where it is deployed.
Architecture overview
In this architecture, Consul serves as the source of truth for your entire data center, tracking available endpoints, service configuration, and secrets for TLS encryption. New applications and services automatically register themselves with Consul using the Consul agent or API. When a request is sent through Ambassador Edge Stack, Ambassador Edge Stack sends the request to an endpoint based on the data in Consul.
Installing consul
In this guide, you will register a service with Consul and use Ambassador Edge Stack to dynamically route requests to that service based on Consul's service discovery data. If you already have Consul installed, you will just need to configure the ConsulResolver in the Configuring Ambassador Edge Stack section.
Before we install Consul, make sure to check the Consul documentation for any setup steps specific to your platform. Below you can find setup guides for some of the more popular Kubernetes platforms. This step is primarily to ensure you have the proper permissions to set up Consul, and can be skipped if your cluster has the necessary permissions already. This page will walk you through the process of installing Consul
- Microsoft Azure Kubernetes Service (AKS)
- Amazon Elastic Kubernetes Service (EKS)
- Google Kubernetes Engine (GKE)
Add the Hashicorp repository for installing Consul with Helm. If you do not have Helm installed, you can find an installation guide here.
Create a new YAML file (eg.
consul-values.yaml) for the Consul installation values and copy the values below into that file:Note: you are free to change the value of the
datacenterfield in the install values. This will be the name of your Consul Datacenter.Install Consul with Helm using the
consul-values.yamlvalues file we just created.
Configuring Ambassador Edge Stack
Deploy Ambassador Edge Stack. Note: If you do not have Ambassador Edge Stack deployed into your cluster, head over to the quick start guide before continuing with this section further.
Configure Ambassador Edge Stack to look for services registered to Consul by creating the ConsulResolver. Create a file (eg.
consul-resolver.yaml) and copy the following code into that file:Note: If you changed the name of your
datacenterin the Consul install values, make sure to change it in the resolver above to match the name of your datacenter.If you changed the name of the helm install from
hashicorpto another value, make sure to update the value of theaddressfield in your resolver to match it.If you are having trouble figuring out what your
addressfield should be, it follow this format:http://{consul server pod}.{consul server service}.{namespace}.svc.cluster.local:{consul port}. The default Consul port should be8500unless you changed it.This will tell Ambassador Edge Stack that Consul is a service discovery endpoint.
Apply this configuration to your cluster with:
The ConsulResolver is Opt-In. In other words, after applying the ConsulResolver you need to add
resolver: consul-dc1in each Mapping that you want to use this resolver for. Otherwise it will use your default resolver, and the service associated with that Mapping will not be registered in Consul.For more information about resolver configuration, see the resolver reference documentation. (If you're using Consul deployed elsewhere in your data center, make sure the
addresspoints to your Consul FQDN or IP address).
Routing to consul services
You'll now register a demo application with Consul, and show how Ambassador Edge Stack can route to this application using endpoint data from Consul. To simplify this tutorial, you'll deploy the application in Kubernetes, although in practice this application can be deployed anywhere in your data center (e.g., on VMs).
Deploy the Quote demo application. Create a file (eg.
quote.yaml) and copy the following code into it:
The Quote application contains code to automatically register itself with Consul, using the CONSUL_IP and POD_IP environment variables specified within the Quote container spec.
Apply this configuration to your cluster by running:
This will register the quote pod as a Consul service with the name
quote-consuland the IP address of the quote pod.
The
"consul.hashicorp.com/connect-inject": "false"annotation tells consul that we do not want to use a Consul-Connect sidecar to register this service. Without a Consul-Connect sidecar to proxy requests, the service needs to include code to make a request to Consul to register the service. We include the environment variablesCONSUL_IP,POD_IP, andSERVICE_NAMEto provide the Quote service with enough information to build that request and send it to Consul. If you would like to see how that code works, please check out our repo for the Quote service. Later in this guide we will show how to configure Consul-Connect as well.
- Verify the quote pod has been registered with Consul. You can verify the quote pod is registered correctly by accessing the Consul UI.
Go to http://localhost:8500/ from a web browser and you should see a service named quote-consul.
Create a new YAML file (eg.
quote-mapping.yaml) for thequote-consulservice:Install the mapping to your cluster by using the following command:
Note that in the above config:
servicethe service name you specified in the quote deploymentresolvermust be set to the ConsulResolver that you created in the previous stepload_balancermust be set to configure Ambassador Edge Stack to route directly to the Quote application endpoint(s) that are retrieved from Consul.
Send a request to the
quote-consulAPI.
Consul connector and encrypted TLS
Ambassador Edge Stack can also use certificates stored in Consul to originate encrypted TLS connections from Ambassador Edge Stack to the Consul service mesh. This requires the use of the Ambassador Edge Stack Consul connector. The following steps assume you've already set up Consul for service discovery, as detailed above.
The Ambassador Edge Stack Consul connector retrieves the TLS certificate issued by the Consul CA and stores it in a Kubernetes secret for Ambassador Edge Stack to use. Deploy Ambassador Edge Stack Consul Connector with
kubectl:
This will install into your cluster:
- RBAC resources.
- The Consul connector service.
- A TLSContext named
ambassador-consulto load theambassador-consul-connectsecret into Ambassador Edge Stack.
Deploy a new version of the demo application, and configure it to inject the Consul sidecar proxy by setting
"consul.hashicorp.com/connect-inject"totrue. Note that in this version of the configuration, you do not have to configure environment variables for the location of the Consul server. Create a file (eg.quote-connect.yaml) and copy the following code into it:Apply the demo application to your cluster with the command:
This will deploy a demo application called
quote-connectwith the Connect sidecar proxy. The Connect proxy will register the application with Consul, require TLS to access the application, and expose other Consul Service Segmentation features.Setting the annotation
consul.hashicorp.com/connect-injecttotruein this deployment tells Consul that we want to use the Consul Connect Sidecar.The sidecar proxies requests to the service it is attached to. This is something to keep in mind when you are debugging requests to the service.
Verify the
quote-connectapplication is registered in Consul by accessing the Consul UI onhttp://localhost:8500/after running:You should see a service registered as
quote. It gets its name from the contaner's name property we defined in the YAML above.
Create a file (eg.
quote-connect-mapping.yaml) and copy the following code into it. Create a Mapping to route to thequoteservice in Consul.servicemust be set to the name of the Consul sidecar service. You can view this withkubectl get svc -Ait should follow the format of{service name}-sidecar-proxy.resolvermust be set to the ConsulResolver created when configuring Ambassador Edge Stacktlsmust be set to the TLSContext storing the Consul mTLS certificates (e.g.ambassador-consul)load_balancermust be set to configure Ambassador Edge Stack to route directly to the application endpoint(s) that are retrieved from Consul
This will create a Mapping that routes to the
quoteservice in Consul.Apply the mapping to your cluster with:
Send a request to the
/quote-connect/API.
Environment variables
The Consul Connector can be configured with the following environment variables. The defaults will be best for most use-cases.
| Environment Variable | Description | Default |
|---|---|---|
| _AMBASSADOR_ID | Set the Ambassador ID so multiple instances of this integration can run per-Cluster when there are multiple Ambassador Edge Stacks (Required if AMBASSADOR_ID is set in your Ambassador Edge Stack deployment) | "" |
| _CONSUL_HOST | Set the IP or DNS name of the target Consul HTTP API server | 127.0.0.1 |
| _CONSUL_PORT | Set the port number of the target Consul HTTP API server | 8500 |
| _AMBASSADOR_TLS_SECRET_NAME | Set the name of the Kubernetes v1.Secret created by this program that contains the Consul-generated TLS certificate. | $AMBASSADOR_ID-consul-connect |
| _AMBASSADOR_TLS_SECRET_NAMESPACE | Set the namespace of the Kubernetes v1.Secret created by this program. | (same Namespace as the Pod running this integration) |
More information
For more about Ambassador Edge Stack's integration with Consul, read the service discovery configuration documentation.








